Multi-factor authentication (MFA) is an effective security measure that requires users to provide multiple forms of identification before accessing an account or system. Unlike relying solely on passwords, which can be vulnerable to cyber attacks, MFA adds an additional layer of protection. This way, even if a password is stolen, unauthorised individuals will face difficulty accessing sensitive information.
In this article, we take a look at the multi-factor authentication (MFA) meaning in more detail, explain how it works and discuss key MFA methods.
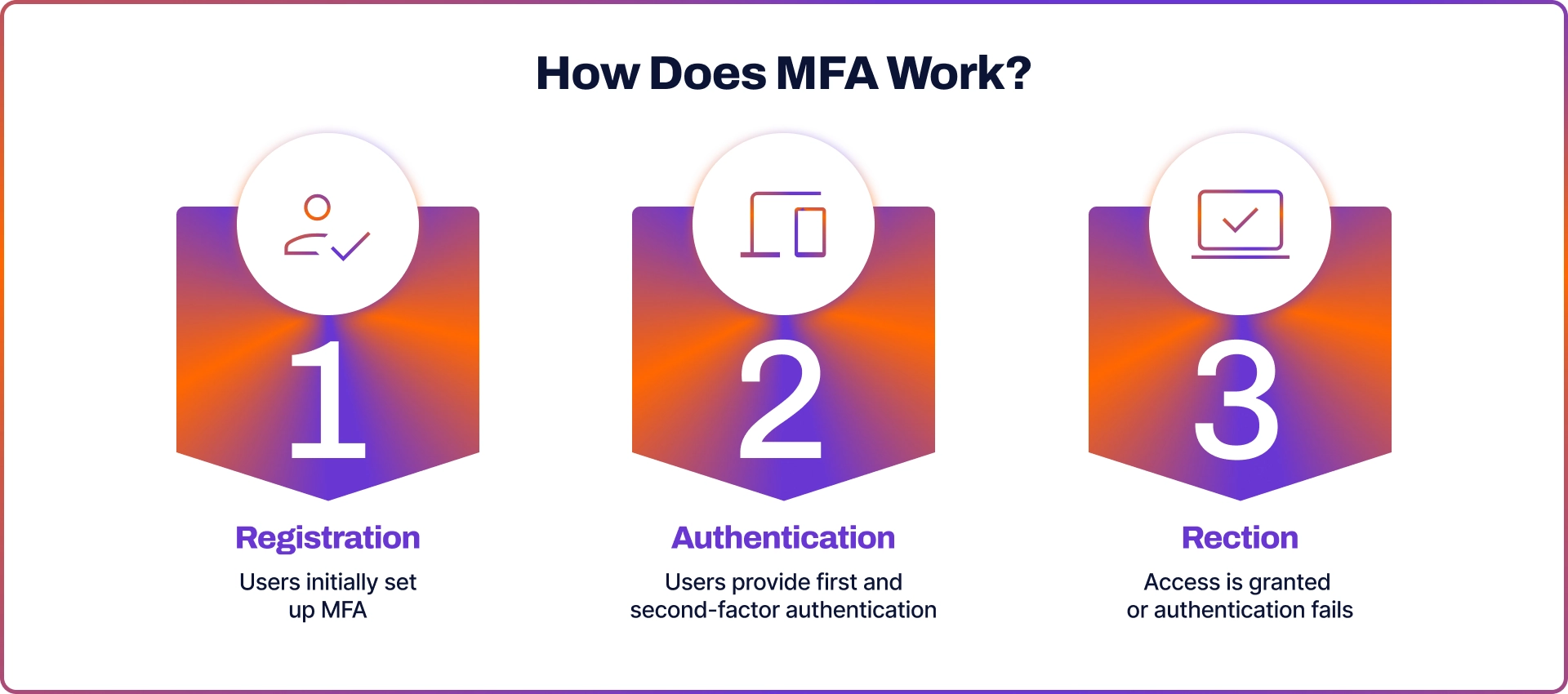
How Does MFA Work?
The MFA process is typically broken down into three steps:
- Registration: Users initially set up MFA by providing the required authentication methods, such as setting up a fingerprint scan or linking a mobile number.
- Authentication: When accessing a system, users must provide the necessary credentials. This could be a combination of a password, a one-time code sent to their phone, or a biometric scan.
- Reaction: If the authentication fails, the system will deny access and may trigger additional security protocols, like notifying the user or locking the account.
MFA Methods
MFA employs various methods to verify a user's identity.
Knowledge Factor
The knowledge factor is centered around the information that a user can remember. This type of authentication is the most conventional method and includes the following:
- Password: A password is a confidential sequence of characters that a user selects and remembers for accessing various accounts. It is crucial to create strong, distinctive passwords for each account to enhance security measures.
- Personal Identification Number: PIN is a numerical code that users must remember. It is typically employed for banking transactions or unlocking devices.
- Security Questions: These are personalised questions that users set during the creation of their accounts. Examples include asking about a user's first school, favourite book, or mother's maiden name. They serve as additional measures to verify identity in case a user forgets their password.
Possession Factor
The possession factor involves using physical items or devices as an additional layer of authentication. This means that even if someone knows your password, they cannot access your account without these specific possessions. Examples of such items include:
- Security Token: A security token is a compact hardware device that generates a unique authentication code at regular intervals. To access a system or platform, users must enter this code in addition to their password.
- Smartphone: The advent of mobile technology has made smartphones an essential tool for authentication. They can conveniently receive one-time passwords (OTPs) through SMS or utilise apps that generate authentication codes.
- Smart Cart: A smart card refers to a card that contains a built-in chip, much like a credit card. This chip enhances security by adding an extra layer of protection during the authentication process when it is inserted into a reader.
Inherence Factor
Inherence factor is one of the most personal authentication methods available as it relies on biometric data involving unique biological traits of the user. Some examples of biometric verification include:
- Fingerprint Scan: Each person has a distinct pattern of fingerprints. Devices that are equipped with fingerprint scanners utilise this pattern to authenticate the user's identity.
- Facial Recognition: By using cameras and sophisticated algorithms, these systems can accurately map and identify the distinct contours and characteristics of an individual's face.
- Voice Authentication: This method examines and analyses the unique voice patterns and pitch of the user. It is particularly beneficial for systems that operate through phone-based interfaces or smart home devices.